Similar Posts

VMware Cloud Foundation Orchestrator User Interaction — part 1
Have you ever wished that instead of failing, a workflow could prompt you for a missing…
What Is an MCP Server, and Why Should Marketers Care?
MCP (Model Context Protocol) connects your AI tools directly to your marketing stack—your CMS, analytics, CRM,…

Phone thieves caught on CCTV!
This group are called Tech Harbour Services and they’re located on New Garden Town in Lahore,…
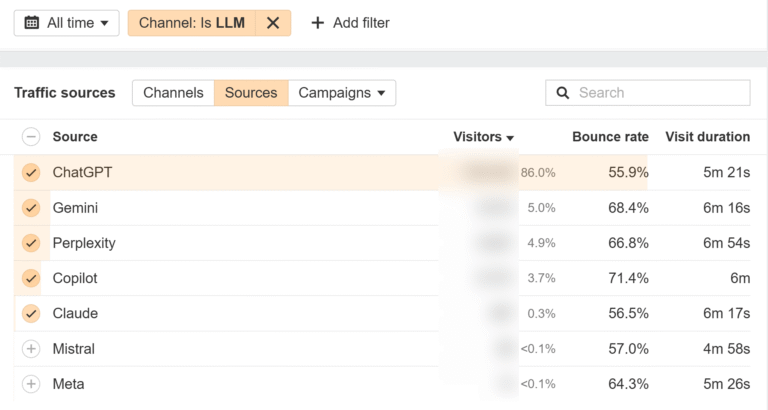
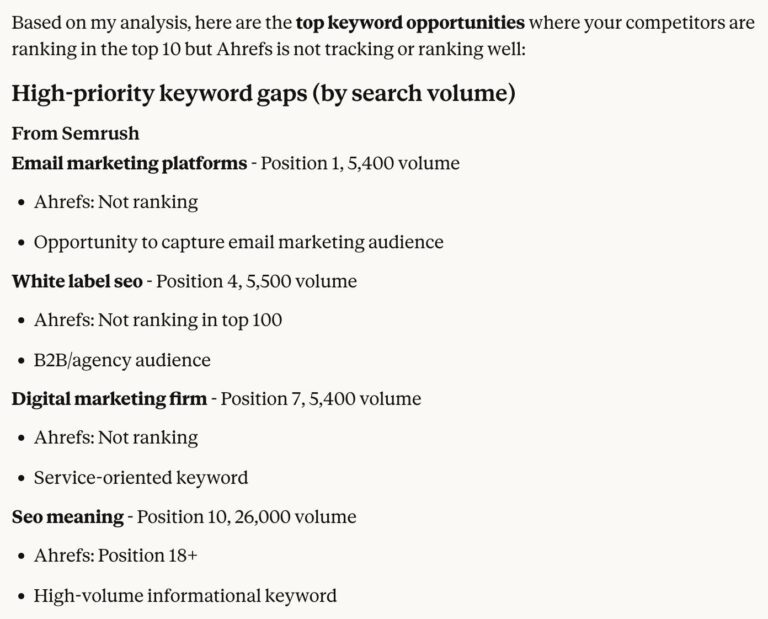
Generative Engines Are Breaking Web Analytics and Hurting Their Future
Search is moving from traditional search engines to generative engines, but traffic from many of these…

NSX Application Platform Deployment with an HTTP/HTTPS Web Proxy – Part 1
Welcome to another blog post on NSX Application Platform (NAPP). Over the last few weeks, I…
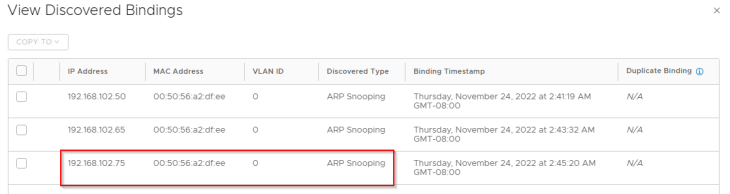
NSX Security : Trust on First Use (TOFU) and Trust on Every Use (TOEU) Explained
When dealing with Spoofguard, address learning and distributed firewall (DFW), we need to consider two modes…